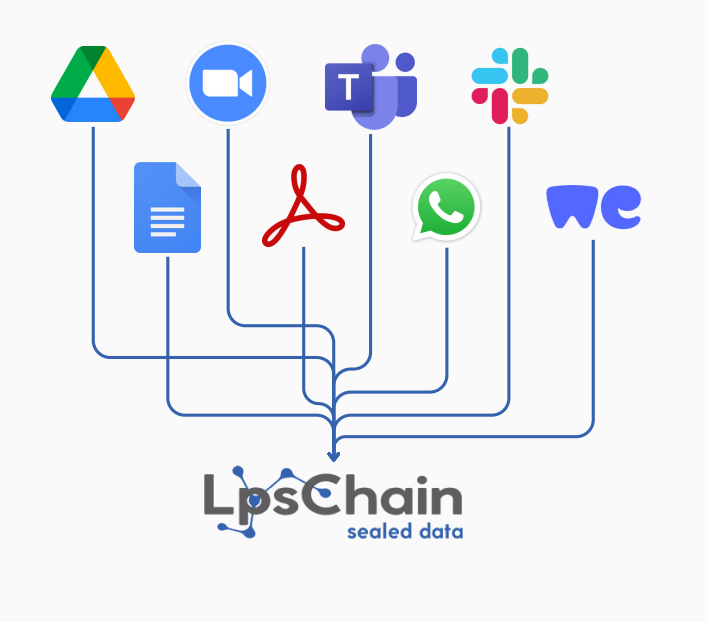
With blockchain and post-quantum-based encryption infrastructure, your data is securely stored, transmitted, and monitored. It enables you to securely manage both internal and external business processes on a single platform with features such as e-signature, workflow management, end-to-end encrypted chat and video conferencing, synchronized collaborative workspaces, and multi-device support.

• Immutable audit logs based on blockchain technology
• Post-quantum secure encryption infrastructure
• Secure file sharing and data transfer
• Access control and authorization management
• Synchronized collaborative workspaces
• Centralized storage and data management
• API integrations (AD, DLP, SIEM, SOAR, Sandbox, etc.)
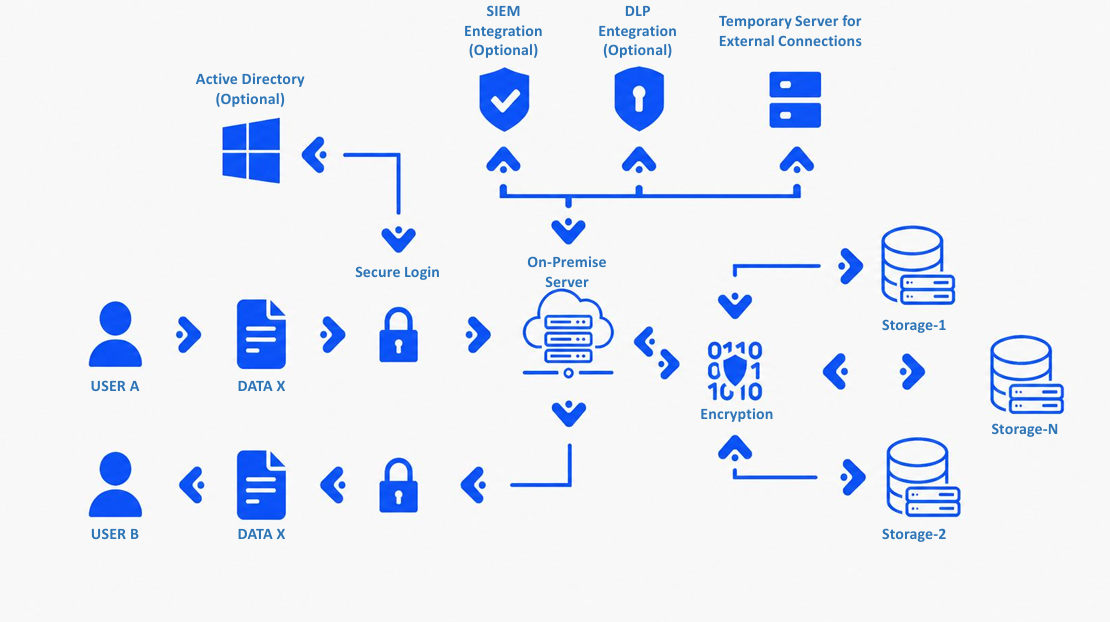
How Does It Work?
LpsChain integrates with existing IT infrastructures without requiring architectural changes. With Active Directory integration, secure login mechanisms, and a centralized server architecture, users can access data within their authorized permissions; all data transfers are encrypted and recorded in an auditable manner.
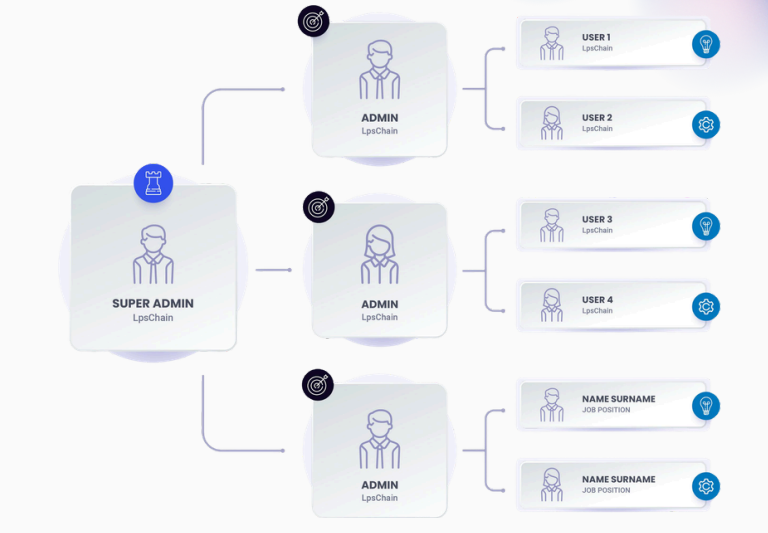
Tenant & Multi-Space Architecture
The platform’s multi-tenant architecture enables different organizations, units, or projects to operate in complete isolation on the same infrastructure. Each tenant is independently managed with its own users, access permissions, data, and security policies, while central system administrators can oversee the entire structure from a single point. This architecture provides scalability, security, and operational flexibility, making it ideal for both large organizations and multi-stakeholder projects.
Secure File Sharing, Integration, and Authorization
The platform integrates at the API level with Active Directory, DLP, Anti-Virus, SIEM, SOAR, Sandbox, Office 365, and third-party applications, ensuring full compatibility with the existing security ecosystem. File sharing is carried out with end-to-end encryption through dynamic data transfer within the organization, project-based workspaces, and external source connections. File owners can centrally manage all access and authorization settings, while users can transparently view all changes made within their permissions and audit logs. This creates a secure, traceable, and consistent data-sharing infrastructure across multiple parties.


